…The African region is over-exposed to threats spreading via the Internet, which are the most common initial-access tools for cyber attackers
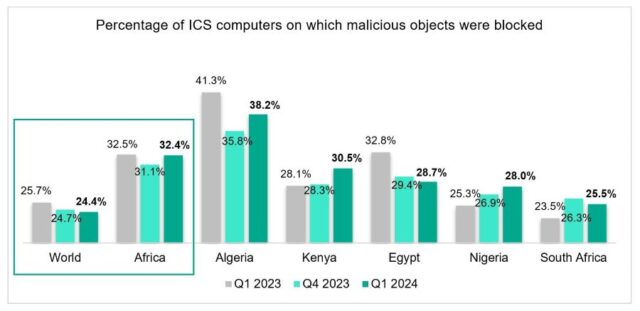
FRI MAY 31 2024-theGBJournal| According to Kaspersky statistics, in the first quarter of 2024, the percentage of Industrial Control Systems (ICS) computers globally on which malicious objects were blocked decreased by 1.3 percentage points (pp) from the first quarter of the previous year – to 24.4%.
In Africa the amount of malware remained almost unchanged, on a level much higher compared to other regions – 32.4% of ICS computers in Africa faced cyberthreats in the first quarter of 2024. In South Africa the figures are 23.5% in Q1 2023 and 25.5% in Q1 2024, Kenya – 28.1% and 30.5%, while in Nigeria – the figures grew from 25.3% to 28%.
In the first quarter of 2024, Kaspersky’s protection solutions blocked malware from 10,865 different malware families of various categories on industrial automation systems. The African region is over-exposed to threats spreading via the Internet, which are the most common initial-access tools for cyber attackers.
The region also leads in charts of malware spread via removable devices (5.6% of ICS computers faced it, compared to the global figure of 1.13%), which is the other way for cyber attackers to try to bypass the safeguards at the perimeter and to spread within the internal infrastructure.
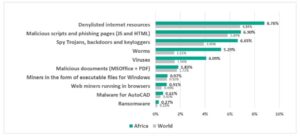
Malicious objects that are used for initial infection of computers include dangerous Internet resources that are added to denylists (this threat was blocked on 8.78% of ICS computers in Africa), malicious scripts and phishing pages (6.9%), and malicious documents (1.83%).
These malicious objects are normally used at the initial phases of the attack chain. As a result, they are blocked by security solutions more often than everything else. This is normally reflected in Kaspersky Security Network statistics.
Malicious objects used to initially infect computers deliver next-stage malware – spyware, ransomware, and miners – to victims’ computers. Spyware (Trojan-Spy malware, backdoors and keyloggers), which is mostly used to steal money or confidential data, is also widespread both globally and in Africa (blocked on 6.65% of ICS computers in Africa).
Worms and viruses are types of self-propagating malware. To spread across ICS networks, viruses and worms rely on removable media, network folders, infected files including backups, and network attacks on outdated software. This type of malware is very active in African countries compared to other regions and global average.
Extremely high rates of self-propagating malware in the region most probably mean there’s a significant portion of OT infrastructure yet to be protected by security solutions (which is where the malware continuously spreads from) and there’s room for improving the overall cybersecurity culture to follow strict cybersecurity policies.
ICS computers in Africa continue to face covert crypto-mining programs – miners in the form of executable files for Windows and web miners, though this type of malware is decreasing in the recent years. If successfully installed these provide cybercriminals steady earnings from using victim’s computer processing power.
Since AutoCAD software is widely used in ICS organisations, cybercriminals also try to make use of this and similar programs creating special malware, detection of which increased in the first quarter of 2024 compared to previous quarters.
The Middle East and Africa lead among regions where ransomware is spread; though not high in numbers (0.28% and 0.27% of ICS computers faced these respectfully), this may pose serious risk to organisations, especially if data encryption scenario is selected by cybercriminals.
“Africa is actively integrating technologies, but it’s important to keep cybersecurity in mind and apply it to both new technologies and currently used solutions. By a security mindset we mean implementing reliable solutions, setting up security policies and educating employees depending on their level of relation with OT. This applies to all infrastructures, but is especially important in operational technology, where risks of material consequences are very high and impact on safety is possible. We hope organisations in Africa will set the stage in the region for a future where technology and security go hand in hand,” says Evgeny Goncharov, Head of Kaspersky’s ICS Cyber Emergency Response Team.
To keep ICS computers protected from various threats, Kaspersky experts recommend:
Using security solutions for operation technology endpoints and networks, such as Kaspersky Industrial CyberSecurity to ensure comprehensive protection for all industry critical systems.
Regularly updating operating systems and application software that are part of the enterprise’s industrial network. Apply security fixes and patches to ICS network equipment as soon as they are available.
Conducting regular security audits of operation technology networks to identify and eliminate security issues.
Undertaking dedicated ICS security training for IT security teams and OT engineers, which is crucial to improve responses to new and advanced malicious techniques.
Using ICS network traffic monitoring, analysis and detection solutions for better protection from attacks potentially threatening technological processes and main enterprise assets.
Protect IT infrastructure using solutions for timely detection of cyberthreats, investigation, and effective remediation of incidents, such as Kaspersky Next.
Providing the security team responsible for protecting industrial control systems with up-to-date threat intelligence. ICS Threat Intelligence Reporting service provides insights into current threats and attack vectors, as well as the most vulnerable elements in OT and industrial control systems and how to mitigate them.
X-@theGBJournal|Facebook-the Government and Business Journal|email:gbj@govbusinessjournal.com|govandbusinessj@gmail.com